In this post we will cover:
- Our expectations from SDK partners
- What happens when they are not met? Terminated partnership examples
- What major antivirus engines have to say about Bright Data Network products
- Bright Data’s bottom line partnership commitment
Our expectations from SDK partners
Here is Bright Data’s ideal SDK partner app profile:
- A high-quality application that provides real added value to its users, doing what it publicly states it does, and nothing else.
- Employs dedicated developers who ensure that there is a quality User Interface (UI), as well as no bugs, scanning for antivirus (AV) detections and making sure that there are no security risks (such as back doors).
- Complies with security industry standards, such as:
- Enabling users to opt-out at any time.
- Employing a zero-malicious advertising policy.
- Including the developer’s digital signature.
What happens when they are not met? Terminated partnership examples
One: A file sharing application
Partner behavior: As part of a security upgrade, SDK partners were asked to sign their application with a verified digital signature. This is (a common authentication method used by software developers that adds an element of trust and security for app users). The developer in question did not agree to sign his application.
Outcome: Bright Data’s SDK team explained to the partner the benefits of signing the application, but they refused to sign it. We decided to terminate the agreement with this developer, as they were not willing to implement Bright Data’s industry-standard precautions.
Two: A media editing application
Partner behavior: After a few months of working with Bright Data, the developer added a new advertising network, which sometimes displayed advertisements that led users to unverified websites. The partner claimed they served as a lucrative revenue stream.
Outcome: We decided to terminate the agreement with this partner who was not willing to stop using that specific ad network.
Actions that speak louder than words
The above are just two examples of SDK partnerships that were terminated in order to ensure Bright Data networks and products are safe and compliant with international security standards.
Bright Data preferred terminating these 2 SDK partners, even though they provided over 10% of our Residential peer network. Terminating these partners also had a negative impact on our revenue – but we did it anyway, in order to help maintain a strong cybersecurity moat.
Luckily for both Bright Data and its users, it should be noted that most partners are very collaborative – they follow our guidelines and see the value of working together with us on improving their app’s security.
What major antivirus engines have to say about Bright Data Network products
In today’s peer-to-peer economy, no one cares what a company has to say about themselves – no one wants to be ‘marketed’ a product. What people do respect is when neutral third-parties vet applications.
Here’s a sampling of leading industry software certification company findings regarding EarnApp for developer’s security/compliance track record:
AppEsteem
After a detailed review, AppEsteem certified Bright Data’s EarnApp, confirming it met their requirements and was in compliance with their Master Services Agreement.
In order to complete the AppEsteem certification program, EarnApp underwent the most rigorous compliance review conducted by a team of security analysts. This audit brought about practical, constructive feedback which the EarnApp team implemented, and resulted in us further improving the SDK’s features. The following are just several examples:
One: Improved disclosures and transparency – Including more links to detailed FAQ, EULA, privacy policy, how to uninstall the app, etc.
Two: Consent screen redesign – Enabling users to know exactly what they are agreeing to, with detailed explanations of what their IP address will/will not be used for.
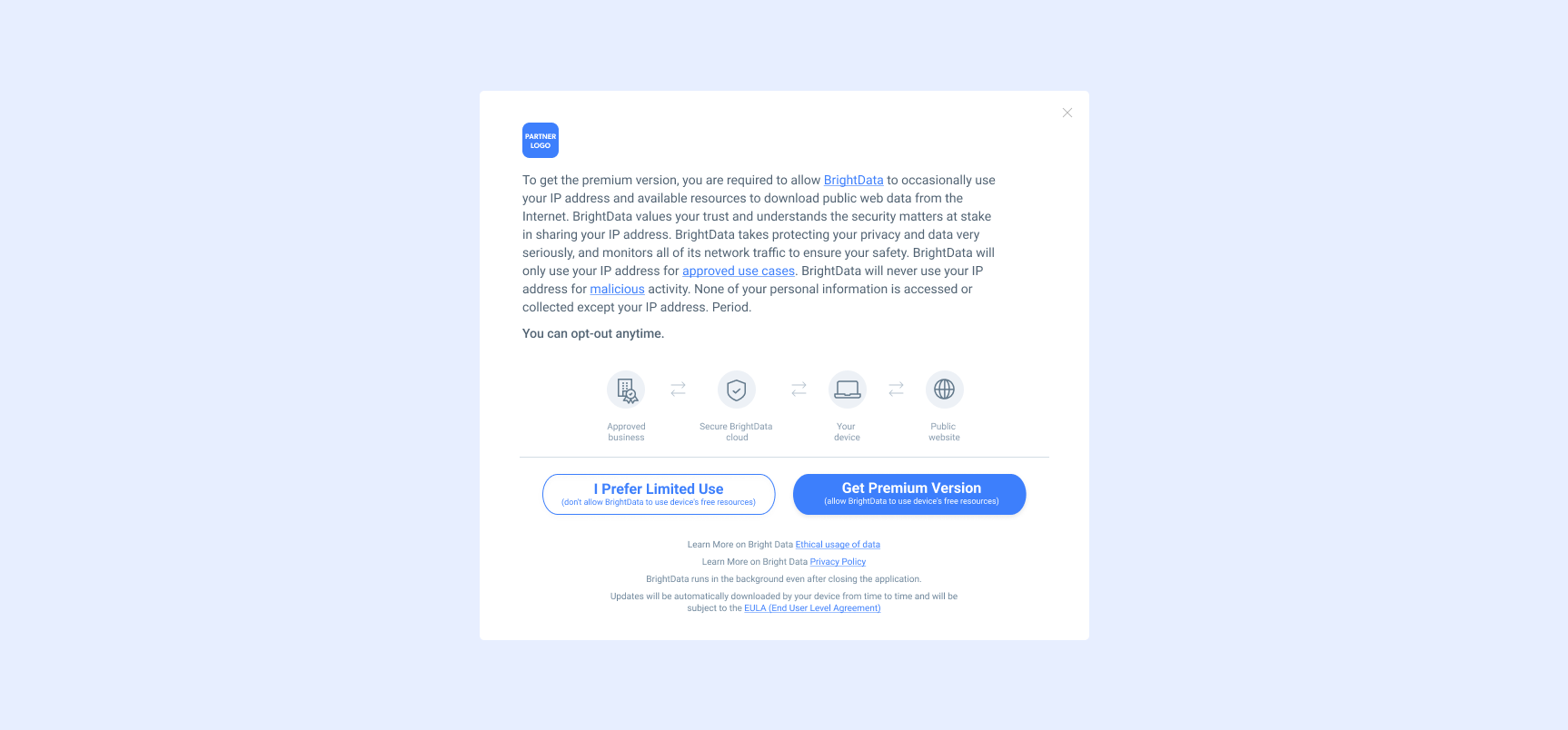
Three: Upgraded digital certificate – Implementing a new Extended Validation (EV) certificate as a signature, for each certified app (EarnApp as well as other SDK partners).

Four: Increasing user visibility –A tray icon appears when the SDK is running in the background.
All existing and new Bright Data SDK partners benefit from the AppEsteem program. Every new partner is now included in the program. Participation is free to the partner; it is paid for by Bright Data.
Kaspersky
Kaspersky detects the general type of technology used by the Bright Data SDK to collect web data, which is called proxy. Furthermore, Kaspersky correctly writes in their knowledge base:
“If a user has installed such a program on his/her computer, or if it was installed by a system administrator, then it does not pose any threat.”
McAfee/GOOGLE/Avast/AVG/Avira
Here is the full list of companies that EarnApp complies with in terms of safety, and security certification:

The list is continuously updated – see the live version here.
Bright Data’s bottom line partnership commitment
Bright Data’s Director of Security Partnerships, Ofir Meir stressed that:
‘The Bright Data SDK is at the heart of what we do. When a user installs an app with our SDK, they put their trust in us. We, therefore, take any concern with the utmost seriousness.
As a rule of thumb, we perform virus sanity checks twice a day, every day. This is in order to ensure that the apps’ users install with Bright’s SDK do not contain anything malicious originating from a third-party source. Any security concern is immediately addressed implementing our real-time network monitoring protocols. In the event that any Bright Data network products are being detected by an antivirus (AV) engine, it is handled on spot with the relevant vendor as a false positive detection.
We share mutual goals with our partners of being able to create additional passive revenue streams while simultaneously feeling secure, operating in an AV-alert neutral environment’.
Interested in becoming a Bright Data SDK partner?